The Trust Layer for Secure Apps and Organizations
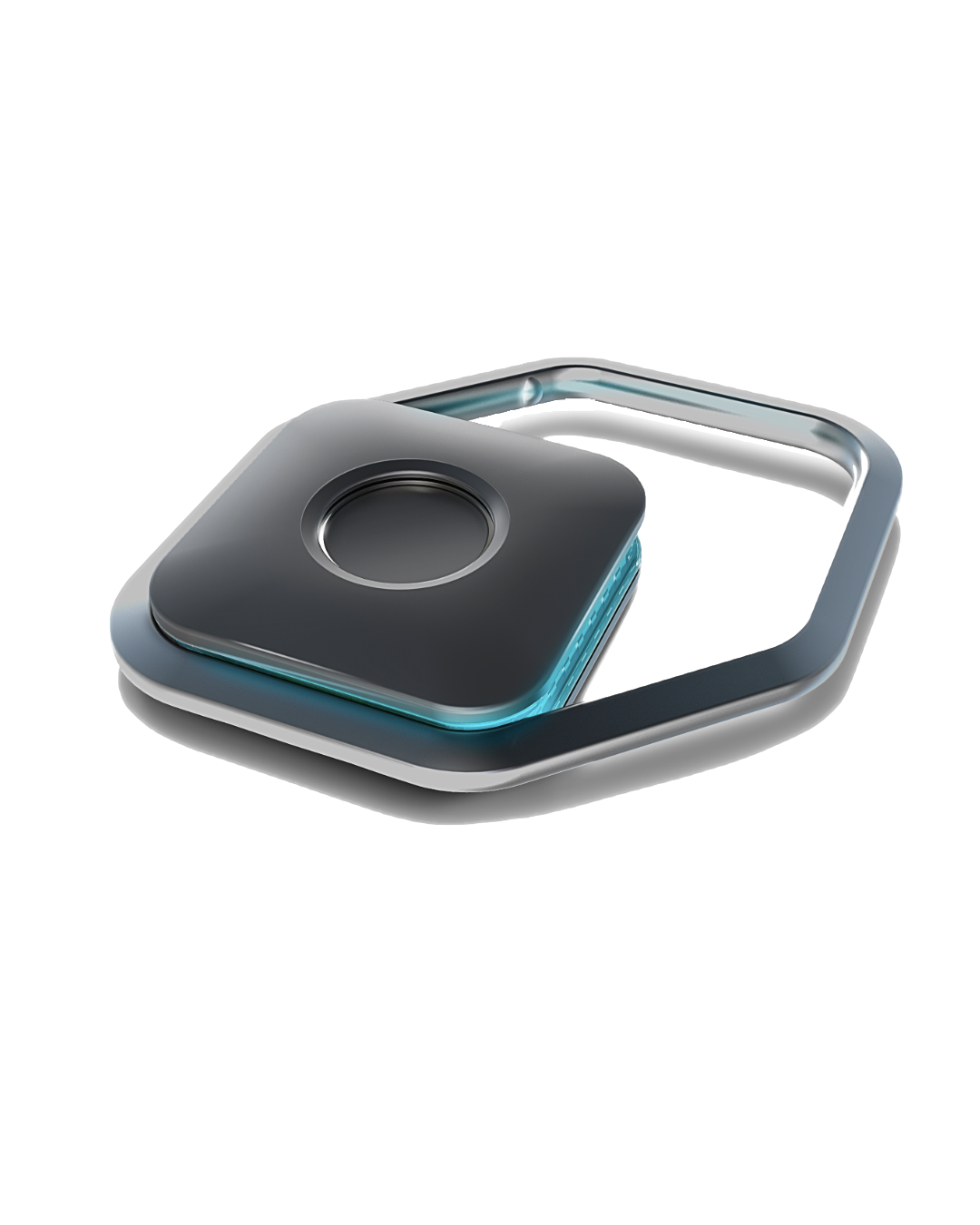
JEM secures your digital estate with two trust tiers: platform biometrics (Touch ID, Face ID, and Android BiometricPrompt) and JEM AirKeys (pictured). Authenticate users, gate sensitive actions by human presence, perform stepped-up authorization, sign and encrypt payloads, all through one API. Shift flows across trust tiers without changing code.
The JEM Platform
Three components. One coherent security layer.
The backbone and authorization server behind the SDK. Handles device enrollment, key distribution, and enterprise lifecycle management. Built on globally available, internet-scale, edge infrastructure. Serverless architecture ensures seamless scalability and fast response times globally.
Ships as part of the JEM SDK. Uses platform biometrics (Face ID, Touch ID, Android biometrics) and the device secure enclave. No additional hardware required. Provides Level 1 biometric-gated security out of the box.
AirKey is a separate physical device with its own biometric-gated crypto enclave, creating an independent trust boundary from the host device. That reduces host-compromise blast radius, supports policy step-up for high-risk actions through the same SDK API, and gives teams a clearer assurance story for security and compliance reviews. It also adds explicit device lifecycle control: enroll, assign, and revoke keys centrally.
Who JEM Is For
Whether you're building an app, running an organization, or managing security services for clients — JEM has a path for you.
For Developers
Integrate JEM into your app with the runtime SDK. Biometric auth, encryption, and signing through a clean API. Available now.
Get SDK accessFor Individuals
Using a JEM-enabled app? Learn what the security guarantee means for you — and try JEMPass, our reference credential manager built entirely on JEM.
Learn moreReady to Build on JEM?
The SDK is available now. JEM AirKey hardware is in stock and ready for deployment. Get in touch and we'll get you started.
Looking for a narrower control? When login is not enough