One Simple API. No Encryption Infra.
Hardware-backed, biometrically-gated encryption in a single function call — with no envelope encryption infrastructure to build and no platform-specific key management to maintain. Ships as software; upgrades to dedicated hardware without changing a line of code.
What JEM Brings to Your App
One SDK. Biometric-gated authentication, encryption, and signing — across every platform your app runs on.
JEM's biometric verification ensures that authentication and encryption functions can only be activated by the registered user. Even if a device is stolen or compromised, protected credentials and data remain inaccessible.
JEM's key operation is O(1) regardless of payload size. The runtime handles bulk encryption locally using JEM-authorized keys, so you get hardware-backed key security without throughput constraints. Call the same API whether you're protecting 32 bytes or a gigabyte.
All sensitive cryptographic operations execute inside JEM — hardware or software. Keys are held ephemerally and never persisted in any usable form. Your API stores only encrypted artifacts; it never sees plaintext.
The JEM runtime abstracts all platform differences. The same developer API runs on Angular web apps, native mobile, Electron desktop, and Node CLI — with platform-appropriate host adapters under the hood. Write once, deploy everywhere.
Use JEM SoftKey (platform biometrics + secure enclave) for standard protection out of the box. When your users or policies require higher assurance, JEM AirKey provides hardware-level security through the exact same API call — no code changes needed.
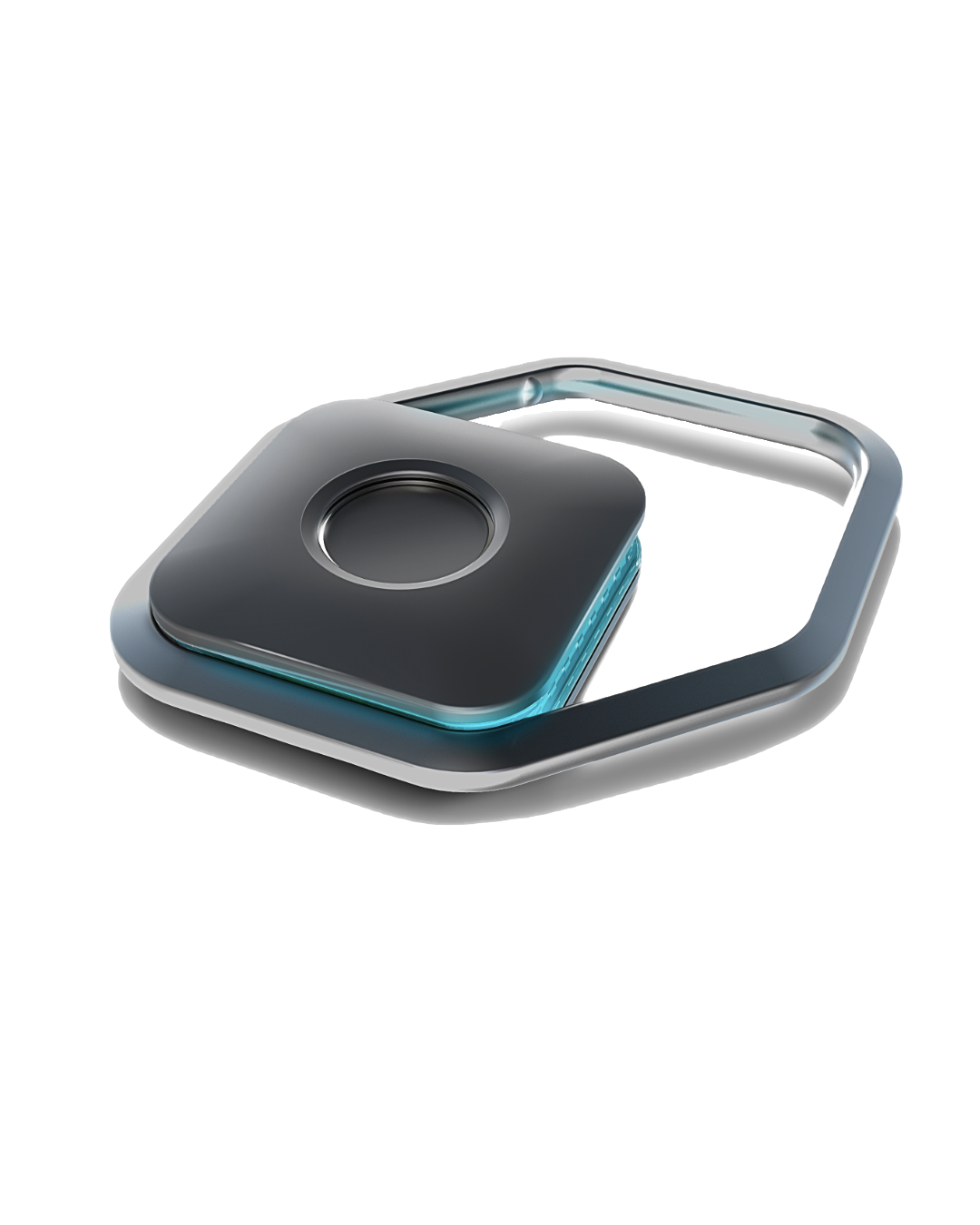
Unlike USB security keys that require drivers and physical access, JEM AirKey communicates wirelessly over BLE. Your app connects automatically. Users carry it on a keychain. No tap required, no middleware to install.
One Call. No Infrastructure Tax.
JEM makes hardware-grade encryption as simple as a single function call — without the envelope encryption library you'd otherwise build from scratch, for every app, on every platform.
Without JEM
Envelope encryption, manually. Per platform. Rebuilt for every app.
// Platform-specific biometric unlock
const kek = await biometricUnlock(userId);
// Generate a per-item symmetric key
const itemKey = generateSymmetricKey();
// Encrypt the data
const ciphertext = aesGcm.encrypt(plaintext, itemKey);
// Wrap the key (your envelope layer)
const wrappedKey = aesGcm.encrypt(itemKey, kek);
// Store both — your schema, your problem
store({ ciphertext, wrappedKey });With JEM
The same call — whether it's a password field or a storage volume, whether JEM is software or hardware.
const encrypted = await jem.encryptWithJEM( plaintext, KeySlot.PassKey // biometrically-gated );
No key generation, wrapping, or storage to manage
Encrypts any payload at hardware speed — a password field or a storage volume
Identical call for JEM SoftKey (software) and JEM AirKey (hardware)
JEM's runtime handles all cryptographic operations on the client — securely, efficiently, at any scale. Your server stores only encrypted artifacts. The keys never leave JEM.
What JEM Gives Your App
Three capabilities. Any combination. One SDK integration.
Passwordless, Phishing-Resistant Auth
Replace passwords with a single biometric touch. JEM issues FIDO2-compatible authentication assertions signed by the user's hardware or software key — there's no credential to steal and no shared secret to breach. Use JEM as your primary authentication mechanism, as step-up MFA, or as a gating challenge for sensitive routes within your app.
Biometric-Gated Encryption & Decryption
Go beyond authentication. Use JEM as a cryptographic execution environment for your most sensitive data. Encrypt any payload — a password field, a private key, a file, a storage volume — and it becomes accessible only after biometric authorization on the user's JEM. The same O(1) API call works at any scale. Level 1 uses platform biometrics; Level 2 requires a JEM AirKey.
Cloud-Native Lifecycle Management
JEM.Network handles the infrastructure your security layer needs: device enrollment, key distribution, auth token issuance, and instant revocation. Lost device? Revoke in seconds from the management console. Employee offboarding? Automated. No on-premise infrastructure required.
Technical Details
Built on peer-reviewed cryptography. Designed for production from day one.
JEM AirKey Hardware
- Form factor: 30mm × 30mm × 11mm
- Biometric sensor: High-precision integrated fingerprint recognition
- Interface: Single button
- Connectivity: Bluetooth Low Energy (BLE)
Cryptographic Execution
- Symmetric encryption: XChaCha20-Poly1305 (AEAD)
- Signing: Ed25519; key exchange: X25519
- Key lifecycle: Root keys and private keys never leave JEM in any form; held ephemerally only
- Libraries: libsodium (peer-reviewed, widely audited)
JEM SoftKey
- Platform: iOS and Android (ships inside your app via the SDK)
- Biometrics: Touch ID, Face ID (iOS); Biometric Prompt (Android)
- Key storage: Platform secure enclave / hardware-backed keystore
- Connectivity: Direct network; no BLE dependency
JEM.Network
- Infrastructure: Edge-hosted on Cloudflare global network
- Latency: Sub-50ms response times globally
- Auth model: Two-tier PASETO tokens — JEM-signed for user assertion, network-signed for API access
- Management: Device enrollment, key distribution, instant revocation, audit logging
Ready to Integrate?
The JEM SDK is available now. Contact us to get access and start building. JEM AirKey hardware is in stock and ready for deployment.